There is often a misconception of the idea of security. Many think security means that your system can’t be hacked, and your personal files are not accessible. Security means that nobody can get your great aunt’s secret banana bread recipe. You can never be too secure, right?
Well, actually you can. There IS such thing as too secure.
The only way to keep a secret is to not tell anyone. The equivalent in our data world might be to not store the data, or unplug the server altogether. How practical is that?
Data Access
Security is more than just keeping the bad guys out. There is no one-size-fits-all, but the right security approach within an organization is always about balance. Ironclad security can actually be a hindrance to business users. Many Cognos users fall in this category. When capabilities and permissions are restricted too tightly, Cognos users may not have access to needed tools, reports, or data.
Unintended Consequences
There are many ways that companies try to optimize the protection of their Cognos environment. For example, forced password changes every few weeks, or providing limited access to critical data. The weakest link in a security system is almost always the user. If password changes are required so frequently, how is a user going to remember the latest edition? Most likely by writing it down on a post-it note, which completely negates the purpose of this security practice. In other words, perhaps by accident, enforcing unnecessarily restrictive policies can often prove ineffective.
Just like a flowing stream will find the least restricted path, so, users will find ways around policies that are overly restrictive.
Efficiency
Similarly, if a user has to answer more questions to access his/her Cognos environment than opening a bank account, valuable time is being wasted.
Empowerment
Of course, it is necessary to protect the assets in your Cognos environment. But, the key is to find a balance between vulnerability and usability. Just as in personal relationships, anything short of total lock-down requires some trust. Giving Cognos users more control over their content proves that you trust them. An employer’s ability to trust their employees goes a long way.
For example, think of the recent few social media mistakes that have been floating around. When the Houston Rockets eliminated the Dallas Mavericks in the NBA post-season, somebody from the Rocket’s organization posted emojis that Dallas deemed “not very classy.”
Houston then issued an apology statement. We’ve all seen the PR expert begging forgiveness after an employee sends an unintentionally inappropriate tweet. The companies who lock down Internet access of their employees are hit harder. The companies who admit to being human and having faults have less hard to fall.
Of course, in addition to weighing vulnerability and access, organizations must also evaluate the potential risk of compromising access to confidential data. We recognize that in some industries there are laws (thankfully!) regulating the protection and safeguard of personal, financial and health care data.
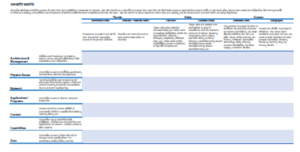
Too often security planners consider only half of the equation. A solution, instead, is to give users enough information that they need to do their job. Here is a security matrix table, with which you can estimate the proper amount of security required by everyone to do their job.
Interested in learning more about security best practices in IBM Cognos? See this recorded webinar.
{{cta(‘7bac48d8-f050-45a6-b7e7-b00be897fab8’)}}

